SEE OUR SECURITY IN ACTION
Upland Trust Center
Upland Trust Center
Security and compliance are ingrained in everything we do, with industry best practices shaping our software development lifecycle.
But don’t just take our word for it – explore the Upland Trust Center to review our security policies, explore product certifications, access key documents, and find answers to common security questionnaire topics.
Proven compliance with industry leading security standards.
Proven compliance with industry leading security standards.
END-TO-END SECURITY
Built for Protection
Built for Protection
We prioritize the confidentiality, integrity, and availability of our customer data.
Here’s how we do it:
- Dedicated Cyber Security Team: Our enterprise grade security and compliance team delivers best-in-class continuous monitoring, proactive risk assessments, and a coordinated method to threat response.
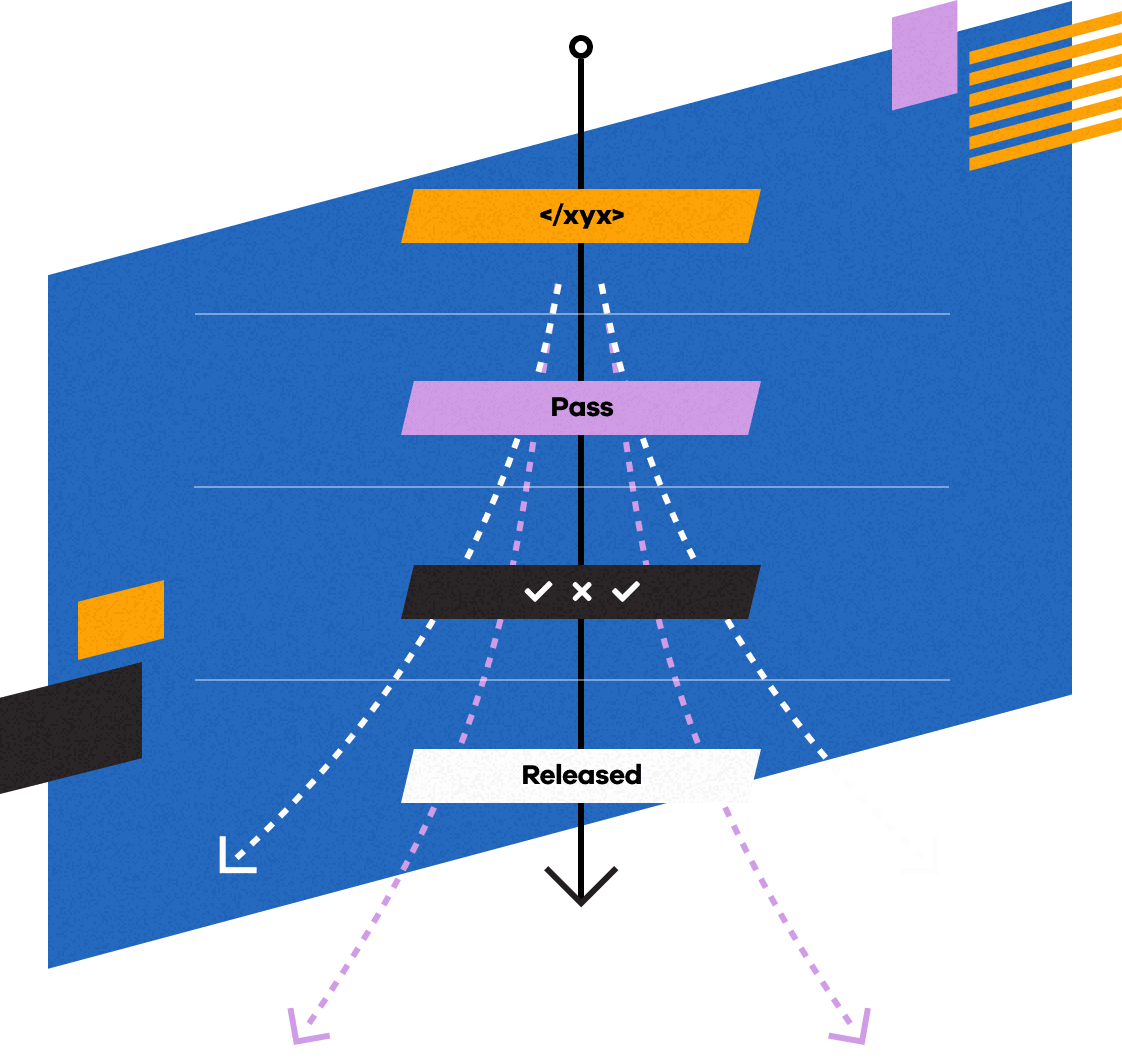
- Secure Product Development: A fortified development lifecycle with built-in protections, automated code scans, rigorous QA, segmented environments, and third-party assessments.
- Protected Operations: Partnerships with Amazon Web Services (AWS), Microsoft Azure, and others provide state-of-the-art datacenters that strive to maintain a global average uptime of at least 99.99%.*
*See Amazon’s Compute Service Level Agreement for more information.