United Wholesale Mortgage Ignites Agent Productivity and Increases NPS with InGenius
United Wholesale Mortgage Ignites Agent Productivity and Increases NPS with InGenius
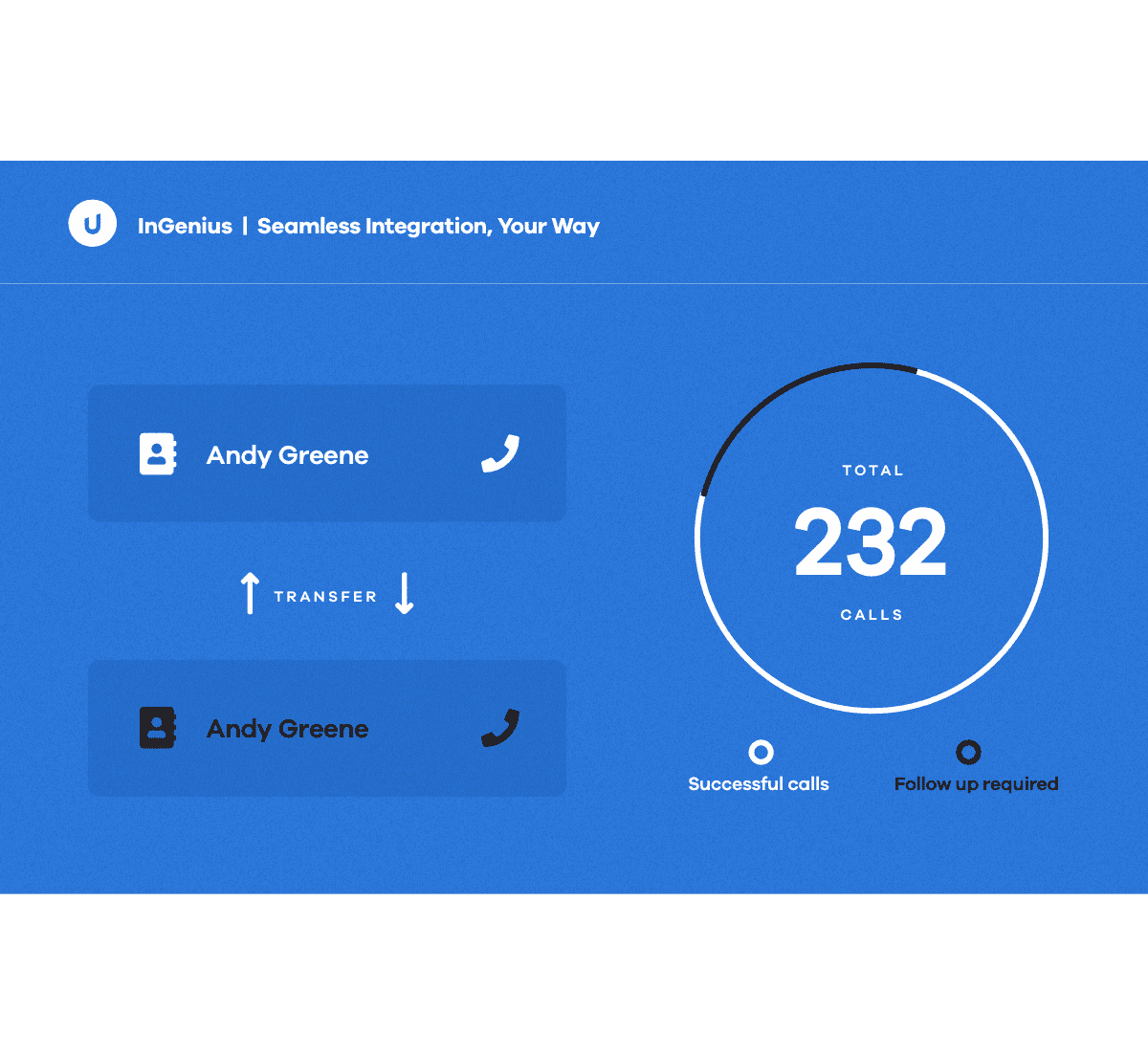
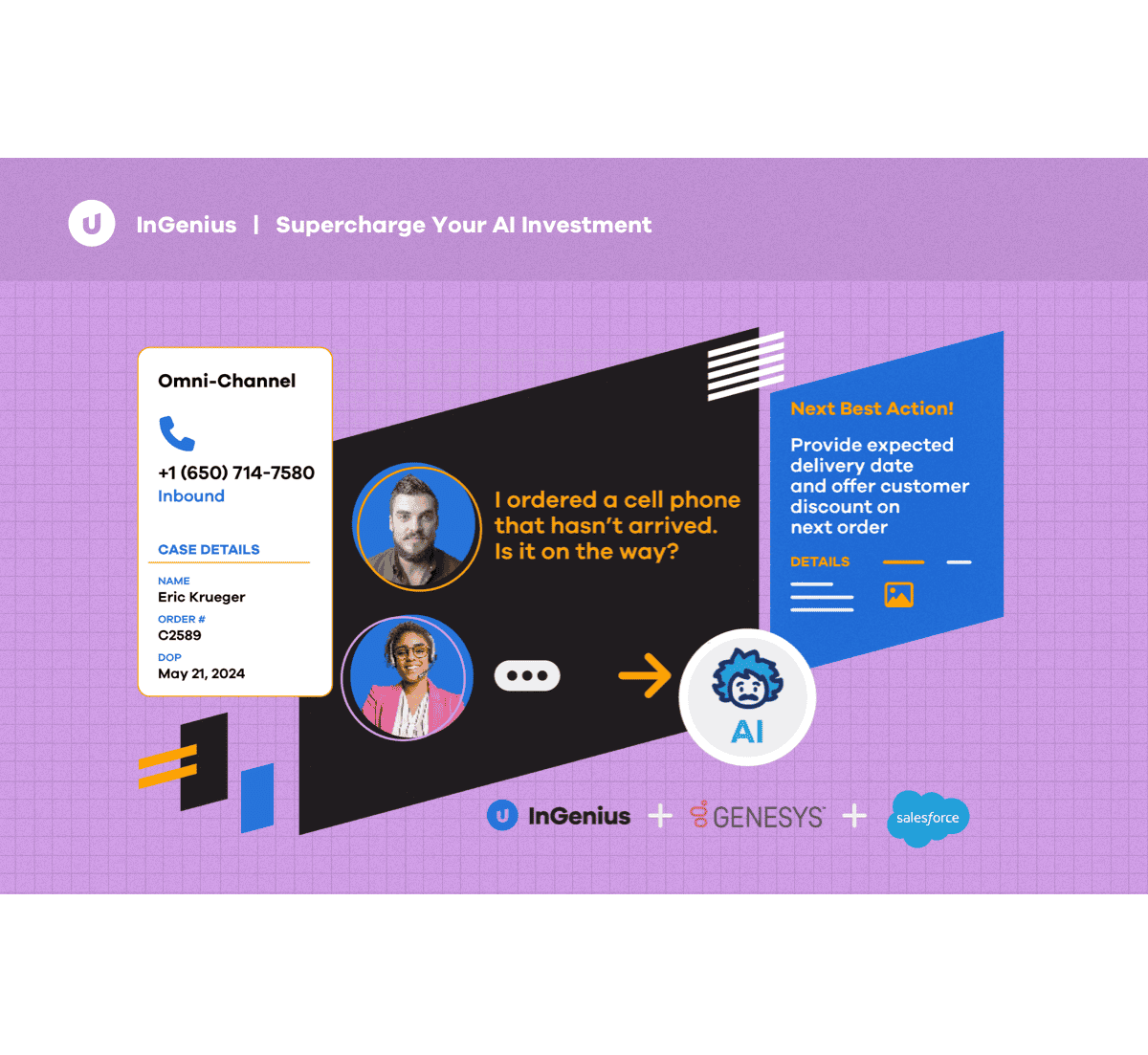
InGenius blended agent and Salesforce Omni-Channel allows each United Wholesale Mortgage agent to handle a combination of calls, chats, and cases. They were able to increase cases handled by 50% and saw a 23% NPS improvement.

Southern Glazer’s Wine & Spirits Wins at Customer Advocacy and Inside Sales
Southern Glazer’s Wine & Spirits Wins at Customer Advocacy and Inside Sales
Southern Glazer’s Wine & Spirits needed a CTI, but wanted a solution that could span multiple teams and complex infrastructure, which consisted of different CRM versions, phone systems, and telephony switches. They implemented InGenius for their inside sales and customer advocacy teams.

Universidad Carlos III de Madrid boosted user experience and operational efficiency
Universidad Carlos III de Madrid boosted user experience and operational efficiency
UC3M used the InGenius CTI integration between Cisco UCCX and Salesforce to improve student and support staff experience. After years of using different systems, they chose to utilize InGenius for a more cohesive process when accessing their information.